An online, managed or remote control backup service offers users using a system for storing and backing up their PC files. On the web backup issuers are business enterprises that provide you with this type of service to customers over the Internet. These on the internet systems almost always run on a schedule, sometimes once a day during the night time whereas computer systems are certainly not being used. Sometimes constructed around a customer software programs program, these backup service providers compress, collect, encrypt and move the info to the remote control backup service provider's servers or off-site hardware.
Insurance Companies
Today�s buyers anticipate even more than quick trouble shooting of gadgets and systems.� They expect assured system availability and all-inclusive aid for the installed products. Distant services play a crucial position in fulfilling the customer expectations. Distant services include repeated monitoring of system conditions and real-time remote entry to customer systems.
How A lot Storage Space Will You Need?
For those using a smaller archive, say a few hundred pictures, a free of charge service may well be all that's needed. MozyHome offers 2GB of space to clients of their freely available edition. This will back up around 500 images from your 10GB decision camera. The nice matters is that you can roll it over into a paid account with almost limitless computer memory for per yr. should you run out of area later. When you've got a huge pic collection with thousands or thousands of hundreds of photos, you may need 1Tb or much more to back it up.
Using this similar example, the technician has already misplaced a couple of hours to travel, now add the actual time expended onsite-and that is right after addressing solely one client's issues. Let's also throw in a lunch hour for our technician, ever since she or he hasn't had just one yet. By the time the technician goes back to the office, she or he might conceivably turn out to be gone for six hours (or more)--yikes! Plus, if you are like most IT enterprise owners, you are paying for the gasoline--and everyone knows that is not getting any cheaper.
The remote service platform may be provided in three assorted connection modes, continuous mode, Ad-hoc mode and disconnected mode. Security is provided with primary significance in remote service platform as the prosperity of the remote control service providers heavily depends on customer adoption.
Console: Avocent’s Cyclades ACS console servers are obtainable in single and dual strength provide options. When combined with incorporated strength administration and centralized administration, these gadgets provide you with secure and consolidated out-of-band infrastructure management. ACS console servers use a Linux operating system, are accessible both in-band and out-of-band, and have detailed logging capabilities and numerous safety features.
Once you start using only our services, you can simply sense a never-before vary in the functionality and effectivity of your company operations. Thus, you are able to serve your customers to their utmost satisfaction.
Lots more revealed about remote management service here.
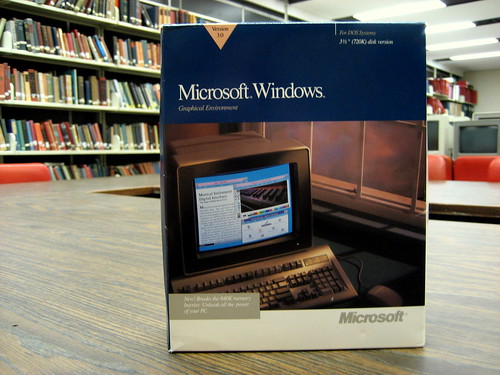
Edgar Eslick is our current Remote Management Service commentator who also reveals techniques usb missile launcher with webcam,microsoft software downloads,avast exchange on their blog.